Cloud Technology: What Do You Get?
The cloud refers to using off site computing resources and storage to supplement or even replace the use of on-site/in-house resources. Instead of buying hardware and software to support your business, you are basically outsourcing this set of tasks.
There are 4 benefits for the small firm and today we will look at the first 2.
Elasticity – With onsite computing, if you need additional capacity you have no choice but to purchase that capacity in discrete steps, which means bearing the costs of being over-capacity for a period of time until growth catches up. Onsite computing also means you must have the capacity to handle your own peak computing and storage demands, and resources may go underutilized much of the time. The cloud allows complete elasticity in the utilization of computing resources. You buy only what you need, as you need it. You can grow or downsize as the business demands.
Pay as you go – On-site hardware involves significant capital expenditures. The cloud allows you to pay for only what you use. The cloud also allows you to benefit from economies of scale that aren’t available using the in-house model. Labor, equipment and maintenance expenses are shared across a vast pool of users.
In the next few weeks, we’ll return to this subject to look at other ways the cloud brings efficiencies to your technology infrastructure that you could never achieve on your own.
What Cloud Technology Means For You–
Recently, we talked about ways the cloud brings value, business protection, and economies of scale to the smaller firm that they could never achieve by themselves. Today, we look at a final benefit of the cloud.
Protection against on-site disaster – If a disaster strikes your physical business location, on-site resources can be damaged, destroyed, or become inaccessible for a period of time. Even if it isn’t a major disaster, if you have a failed server your business could be down for an extended period. When everything occurs in the cloud, you are vaccinated against this type of business calamity. You can still access and use computing resources from anywhere.
In summary, left entirely on its own a small firm just does not have the resources and capital to fully support its own technology infrastructure. The cloud turns that upside down, enabling firms to enjoy the benefits of a fully supported tech foundation without levels of expenditures that are just not feasible for smaller operations.
The Cloud Means No More Stormy Weather
Many small firms are pretty busy handling their own business, and don’t give much thought to what they would do if a natural disaster from a bad snowstorm to much worse hit their physical location and cut power, or physical access to the building. What if the equipment storing all of your data and software needed to run day to day operations became inaccessible? What would happen to your ability to continue to serve your clients or customers?
Though we call it the cloud, with images of gray skies and rain, the cloud can be a ray of sunshine. It is an excellent and cost effective resource for smaller firms to make sure they maintain 24/7 access even in bad weather. Because everything is maintained off site, you can (1) bypass disruption or damage that may have occurred at your physical site, and (2) access what you need to keep your business functioning from any remote location.
Small firms need to realize they are most vulnerable to business disruptions, as they have less capital and fewer resources to carry them through a bad period. The cloud represents a simple and value driven resource to address business continuity issues that could turn a small firm’s business upside down.
Your Front Door is Talking.....Welcome in IoT!
If you’ve been following the news, the Internet of Things (IoT) is getting increasing attention. You’re probably also thinking this is some Silicon Valley fancy thing that will take years to reach the rest of us.
Not really. You probably already have some items of your own tied into the Internet of Things.
First of all, what is the IoT? Simply, it is any object that collects data about itself or its surroundings, and then transfers that data across a network to some other object, which can then make use of that data. For example, if you have a baby monitor that sends crib pictures from upstairs to your phone, you’re tied into the IoT.
But what about business people? Where is it showing up in the workplace? You may have security cameras tied to a network where they can be monitored by a PC or phone. A front door lock that can be remotely opened via phone. A thermostat that can changed by the same phone. Internal lights that go on when you phone approach. All of these are part of the Internet of Things.
If you have questions about whether being tied into IoT presents a data security issue or hacking threat, you should contact a service consultant to discuss these issues. Headlines are now appearing about hacking into the IoT for nefarious purposes. It is a good idea to stay ahead of the curve because as a business, data is a revenue-critical issue. Seriously, you don’t want the front door telling someone your client’s private data.
Data Security: A Formidable Task for Law Firms
By the very nature of their business, attorneys generate data that is very sensitive. As a law firm, you carry a tremendous responsibility to guard that data. These days, technology enables you to store and access information very easily and it also allows you to retrieve it at a moment's notice from remote locations via a variety of different devices. Unfortunately, this convenience can pose a serious challenge to the security of that data. In particular, two security concerns are a breach of data by an unauthorized third party, and the accidental release by authorized users due to human error or carelessness. Of course, it goes without saying that any data breach means considerable liability and a damaged professional reputation. You need efficient IT management that can protect your data and defend your systems against cyber attacks. But who in-house is technically proficient to manage the systems to ensure you're protected 24/7 against all the latest hackers and viruses? Managed IT service companies, known as MSPs, are professionals who can provide solutions for these challenges. Let's look at some of factors that create risks for small- to medium-sized law firms.
- Accessibility: With digital storage, and the decrease in paper storage, legal professionals can now easily gain access to necessary information remotely using a variety of different devices. All of this 24/7 access boosts productivity but it creates new risks that didn't exist when paper files were on-site in locked cabinets. How do you support this remote access without opening up new doors for a data breach?
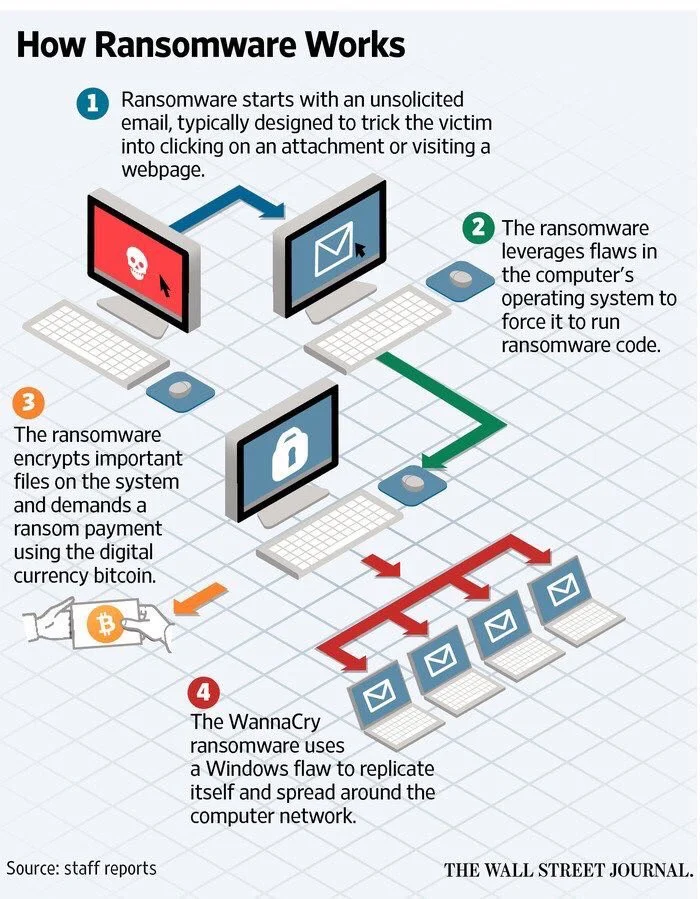
- Growing threats: As cyber criminals constantly devise new ways to hack into systems, your network firewalls have to be updated constantly. No technology, hardware or software can be installed and then forgotten. New viruses and software bugs prompt the need to develop new security patches that have to be installed quickly to keep ahead of with growing s. Staying ahead is a constant battle.
- Multiple locations: As the firm grows so does the IT infrastructure. Even small- to medium-sized law firms may have multiple offices. That means they now have a bigger IT network that becomes more difficult to manage and secure.
- Reliance on technology: With this increasing reliance on technology, your risk of serious business disruption grows if you have any kind of technology failure. Failure can arrive as a data breach, a virus, failed hardware or software, power outage or natural disaster. That means plans for disaster recovery developed by an IT team are very important.
- Limits of in-house support: For most small- to medium-sized firms, there are neither the resources nor the on-going need to have a fully trained support staff available 24/7. You may only have one or two people in this role. As a result, in-house staff may not be able to keep abreast of all the updates and regulatory changes all on their own. Finally, there is one additional limit to in-house support—your own time. You have to supervise them, and its unlikely you have either the background or desire to do that effectively.
- Lack of IT management expertise: Law firms specialize in practicing law. They are not IT specialists. Managing partners remain primarily legal professionals. Their background is not in the management of a technical staff.
Addressing issues: Now we can look for solutions to address the issues discussed above. When it comes to IT management, law firms should have three major goals.
- Data security: Managed IT services can ensure the security of your data because they keep up with new technologies. They will update their software applications as the updates become available. That allows them to meet new challenges posed by cyber criminals.
- Business continuity: Business continuity is very significant for the survival of a business. When your business is disrupted, your fixed costs don't stop, and neither do the demands of your clients. MSPs are full time professionals whose resources you can call on 24/7. They can also develop continuity and recovery plans to protect your business and defend against downtime and outages.
- Cost effectiveness: Like any other business, you are always looking to keep your cost of doing business under control. Since IT is an integral part of your business and you can't do without it, you need to address ways to manage it with the most efficient use of resources. Outsourcing some or all of your IT management can provide resources and availability that is just not possible with an in-house staff. MSPs can provide 24/7 monitoring, technology upgrades, and the depth of expertise and staffing that isn't feasible in the business model of a small- to medium sized business.
In conclusion, we have discussed important aspects of your business and six major issues that present IT management difficulties. You also know which goals you should keep in mind when having your IT networks managed. Managed Services Providers (MSPs) have a business model to help you meet those goals with a long term plan for data security and business continuity.
NPO’s and Volunteer Security Nightmare
Not-for-profits have an unusual issue regarding security. Firms that have trained, paid full-time employees have a strong level of control over the actions of their workers. NPOs, however, may rely heavily on volunteers whose time in the office may be minimal and sporadic. You may feel grateful for their dedication and be less likely to subject them to rigid security training. Also, a threat of punishment for those who make inadvertent errors that create security risks isn't going to be acceptable in the “volunteer” environment.
Though it may seem a waste of precious volunteer time, you need to consider implementing ongoing training and reminders to all volunteers about what they can do to protect your data and digital infrastructure. The 2 most common human errors are falling for phishing scams and bringing storage devices to your office and introducing them to laptops and other devices. Think of the volunteer who creates a brochure for you in their home office, then downloads it to your office PC. This is an excellent backdoor for a virus or malware to break into your infrastructure.
Remind your volunteers on a consistent basis that no outside storage devices are to be brought into the office for use on the NPO’s equipment. Secondly, provide training on how to recognize phishing scams and the risks of opening unfamiliar emails and links. Finally, for volunteers who work from home, consider using safe shared software platforms like Google Drive or Microsoft 365.
SMB- Security and Your Sub-Contractors
So you feel relatively comfortable that you have created cyber security around your data and your employees are trained to avoid security errors in their day-to-day business ( a MAJOR source of security breaches, by the way.) However, you may be overlooking one area where you are exceptionally vulnerable. What protection do you have from those you do business with? If you are a manufacturer, for example, you may have several vendors who provide components and raw materials. How careful are they about data security? Smaller producers and service providers may perceive themselves as not being a likely hacker target, which is incorrect. Small firms are significant targets for data hacking because they have access to larger firms. They can provide a “digital backdoor” to the firms they sell to.
You need to work closely with all of your vendors to ensure that they are as serious about protecting their systems as you are. If you share digital information with your subcontractors, you open a very wide door for any of their vulnerabilities.
And this doesn’t just apply to the manufacturing sector. Medical offices share data, for instance. Consider talking to a security expert to address your vulnerability to a security breach via the very vendors you rely upon. You need to expect as much focus on security from them as you do from yourself.