Social Engineering Inboxes and VoiceMail
Email Threats
Social engineering is non-technical, malicious activity that exploits human interactions to obtain information about internal processes, configuration and technical security policies in order to gain access to secure devices and networks. Such attacks are typically carried out when cybercriminals pose as credible, trusted authorities to convince their targets to grant access to sensitive data and high-security locations or networks.
An example of social engineering is a phone call or email where an employee receives a message that their computer is sending bad traffic to the Internet. To fix this issue, end users are asked to call or email a tech support hotline and prompted to give information that could very likely give the cybercriminal access to the company’s network.
Phishing Email Compromises
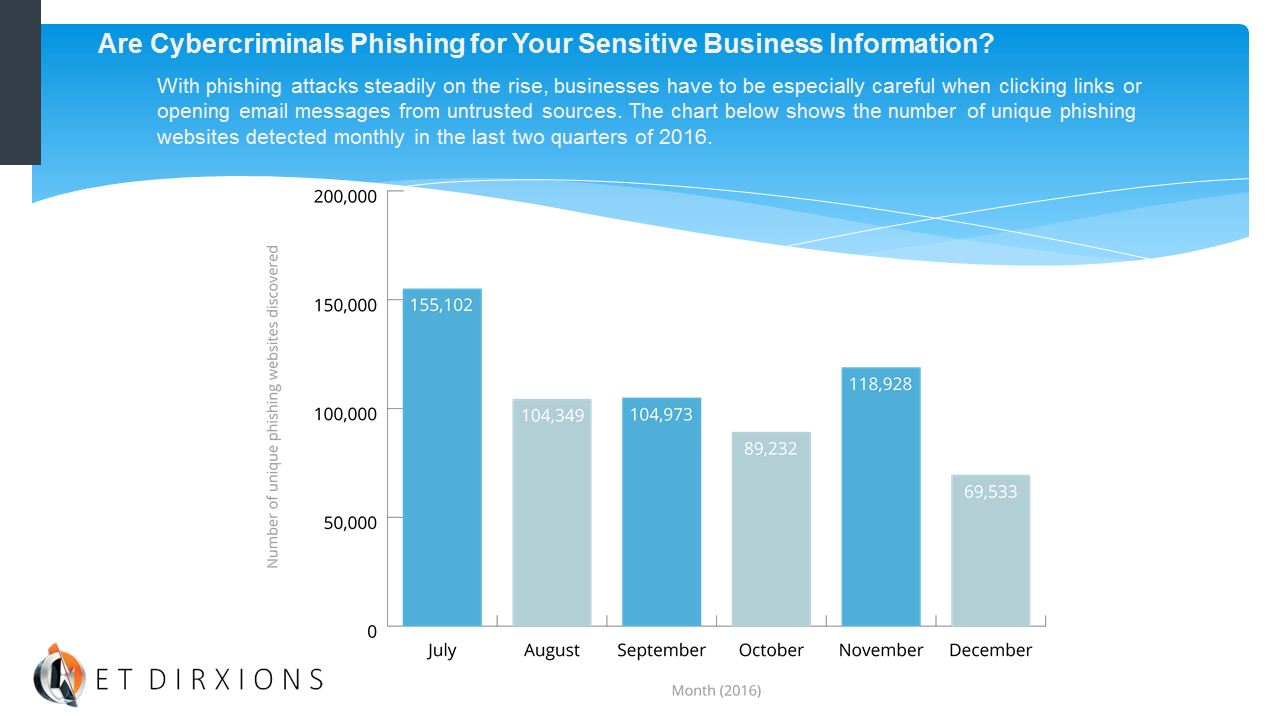
One of the most common forms of social engineering is email phishing—an attempt to acquire sensitive information such as usernames, passwords and credit card data by masquerading as a trustworthy entity. Phishing is likely the #1 primary email threat employees need to focus on.
Such emails often spoof the company CEO, a customer or a business partner and do so in a sophisticated, subtle way so that the victim thinks they are responding to a legitimate request. The FBI says CEO (or C-level) fraud has increased 270 percent in the past two years with over 12,000 reported incidents totalling over $2 billion dollars in corporate losses.
Among the reasons these scams succeed are the appearance of authority—staffers are used to carrying out CEO instructions quickly. That’s why phishing can be so easy to fall victim to.
RSA Conference, “How a Security CEO Fell Prey to Scammers (Almost),” 3/3/2016: http://www.rsaconference.com/blogs/security-ceo-scammers#sthash.egMiB2xW.dpuf
Data Security: Phishing Scams – A People Problem
Phishing Scams – A People Problem
There are some things that only people can fix. There are many security risks to which your data is susceptible, but there is one method that remains a wonderfully effective hacking tool. That is the phishing scam. This is a legitimate looking email that asks the reader to click on a link. If clicked, the link can infect the user’s computer with malicious software that can steal passwords, logins, and other critical data. Alternatively, the email appears to be from a legitimate source, perhaps even duplicating a legitimate webpage. The distinction is that the phishing email asks the user to enter personal information, including passcodes. In either case, that is how hackers easily get into your systems.
What’s the best defense against this one? The single biggest defense is education. Training your people to be constantly wary of all the emails they receive. One way some firms are educating their people is by sending out their own “fake” phishing scams. Employees who click on the link inside are greeted with a notice that they’ve fallen for a phishing scam and then are offered tips how not to be fooled in the future. Think of it as the hi-tech version of Punk’d.
You may not be ready to go that far, but it is important to provide ongoing training to all of your staff about phishing scams. Your staff are all critical factors in your data security plans.
Is That Email a Phishing Scheme?
Research has revealed that over half of all users end up opening fraudulent emails and often even fall for them. Phishing is done with the aim of gathering personal information about you, generally related to your finances. The most common reason for the large number of people falling for fraudulent emails is that the phishing attempts are often so well-disguised that they escape the eyes of a busy email reader. Here are a few tips that help you identify whether that email really came from your bank or is another attempt at defrauding you…
1. They are asking for personal information – Remember, no bank or financial institution asks you to share your key personal information via email, or even phone. So, if you get an email where they ask for your ATM PIN or your e-banking password, something’s amiss.
2. The links seem to be fake – Phishing emails always contain links that you are asked to click on. You should verify if the links are genuine. Here are a few things to look for when doing that:
- Spelling – Check for the misspellings in the URL. For example, if your bank’s web address is www.bankofamerica.com, a phishing scheme email could misspell it is www.bankofamarica.com or www.bankofamerica-verification.com
- Disguised URLs – Sometimes, URLs can be disguised…meaning, while they look genuine, they ultimately redirect you to some fraudulent site. You can recognize the actual URL upon a mouse over, or by right clicking on the URL, and selecting the ‘copy hyperlink’ option and pasting the hyperlink on a notepad file. But, NEVER ever, paste the hyperlink directly into your web browser.
- URLs with ‘@’ signs – If you find a URL that has an ‘@’ sign, steer clear of it even if it seems genuine. Browsers ignore URL information that precedes @ sign. That means, the URL www.bankofamerica.com@mysite.net will take you to mysite.net and not to any Bank of America page.
3. Other tell-tale signs – Apart from identifying fake URLs, there are other tell-tale signs that help you identify fraudulent emails. Some of these include:
- Emails where the main message is in the form of an image, which, upon opening, takes you to the malicious URL.
- Another sign is an attachment. Never open attachments from unknown sources as they may contain viruses that can harm your computer and network.
- The message seems to urge you to do something immediately. Scammers often induce a sense of urgency in their emails and threaten you with consequences if you don’t respond. For example, threat of bank account closure if you don’t verify your ATM PIN or e-banking password.
Finally, get a good anti virus/email protection program installed. It can help you by automatically directing spam and junk mail into spam folders and deactivating malicious attachments.